In the last period I’ve seen a lot of big companies developing their personal Cyber Attack maps. Interesting for me was to find out that even the US and EU governments implied in these projects (probably because they finally understood the importance of cyber security). Below you’ll find a top with the most impressive cyber attack maps.
Top 7 Cyber Attack Maps 2015 – hackingnews.com
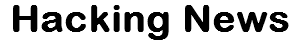
7. CTF365 Cyber Attack Map
Link: https://ctf365.com/pages/map
How it works:
At CTF365, we think real time cyber attack maps are awesome. So we decided to build one of our own. When we started working on our map, we focused on two elements: user experience and information accessibility. By positioning these elements at the foundation of our map, we were able to create a close to real time cyber attack monitoring system that is engaging, interactive, and insightful. It’s more than a map; it’s a window into the core of the CTF365 security training platform.
According to CTF365’s blog, the map is currently being developed, so there might be some problems. But don’t worry, I played a few minutes with the map and it’s working very well. The scope of this map is to act as a comprehensive real time cyber attack monitoring system.
Source – CTF365’s Blog
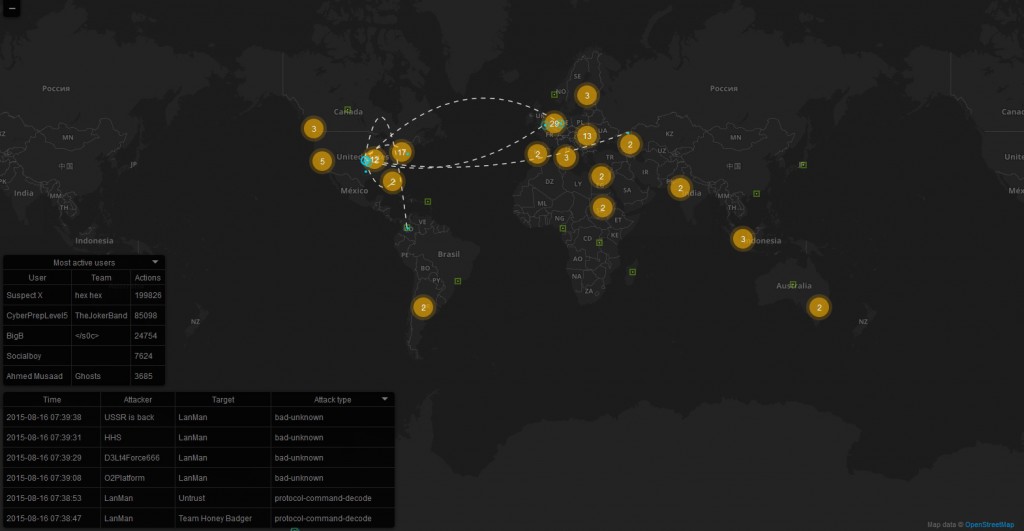
6. Deutsche Telekom Cyber Attack Map
Link: sicherheitstacho.eu
How it works:
- Deutsche Telekom website reports attacks on honeypot systems
- More than 90 sensors worldwide provide an overview of the situation
- New approaches to early prevention of cyber criminality
“New cyber attacks on companies and institutions are found every day. Deutsche Telekom alone records up to 450,000 attacks per day on its honeypot systems and the number is rising. We need greater transparency about the threat situation. With its security radar, Deutsche Telekom is helping to achieve this,”
said Thomas Kremer, Board Member responsible for Data Privacy, Legal Affairs and Compliance.
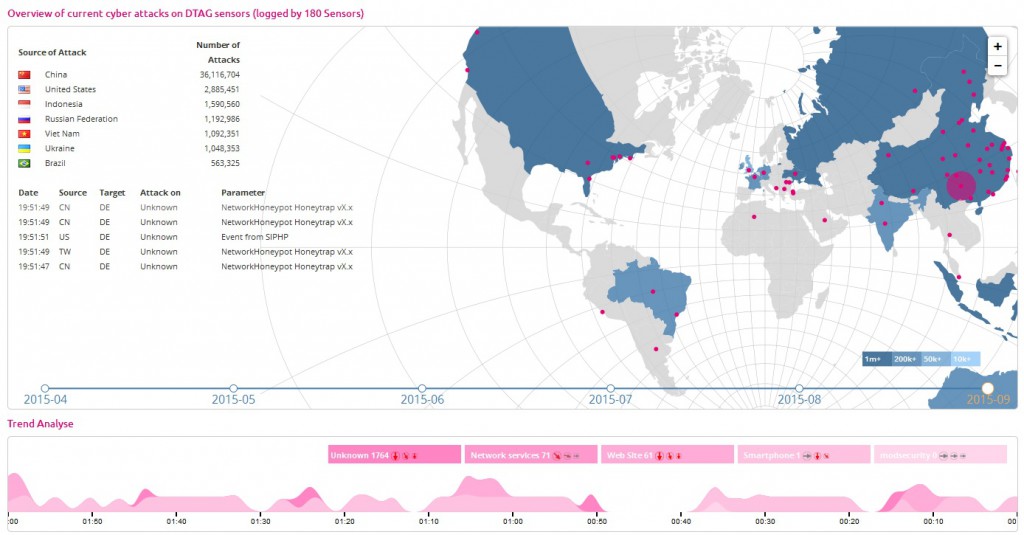
5. Honey Project – HoneyMap

Link: map.honeynet.org
How it works:
The HoneyMap presents real-time attacks against the Honeynet Project’s sensors deployed around the world.
The HoneyMap shows a real-time visualization of attacks against the Honeynet Project’s sensors deployed around the world. It leverages the internal data sharing protocol hpfeeds as its data source.
4. Google Ideas and Arbor Networks – Digital Attack Map
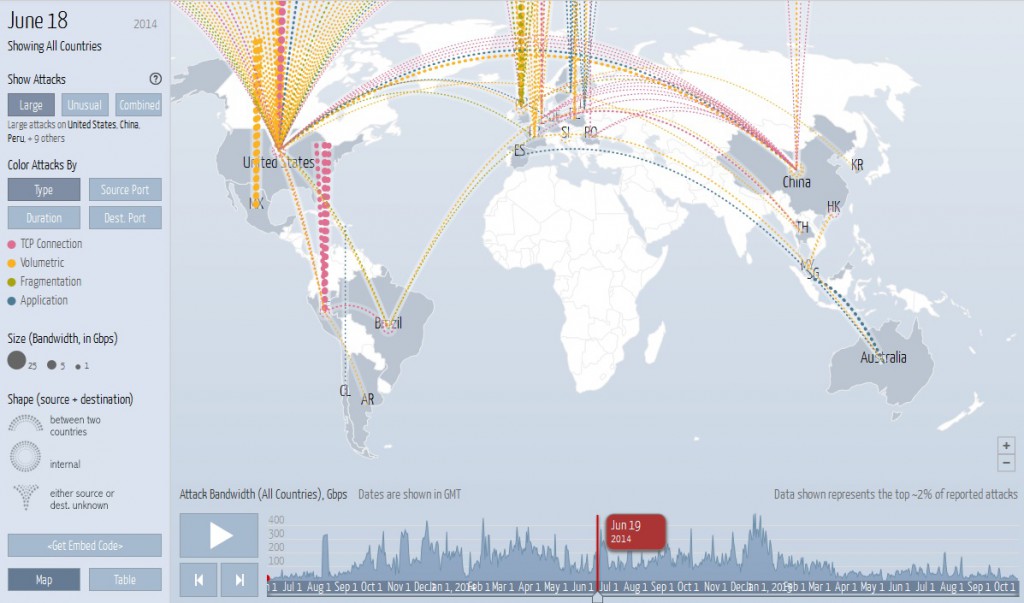
Link: digitalattackmap.com
How it works:
The Digital Attack Map presents data gathered and published by Arbor Networks ATLAS® global threat intelligence system. ATLAS sources its data worldwide from 270+ ISP customers who have agreed to share anonymous network traffic and attack statistics. Data is updated hourly and can also be found in Arbor’s ATLAS Threat Portal. DDoS data ©2013, Arbor Networks, Inc.
Basically, the digital attacking map presents world DDOS attacks (distributed denial of service). These attacks are happening in real time and in the animation you can see the source country and the destination country of the ddos attacks.
To protect your website, you need to have a solution for preventing DDOS attacks. My suggestion for you is to use Cloudflare. It’s free and it works well.
3. Norse Corporation – IPViking Live
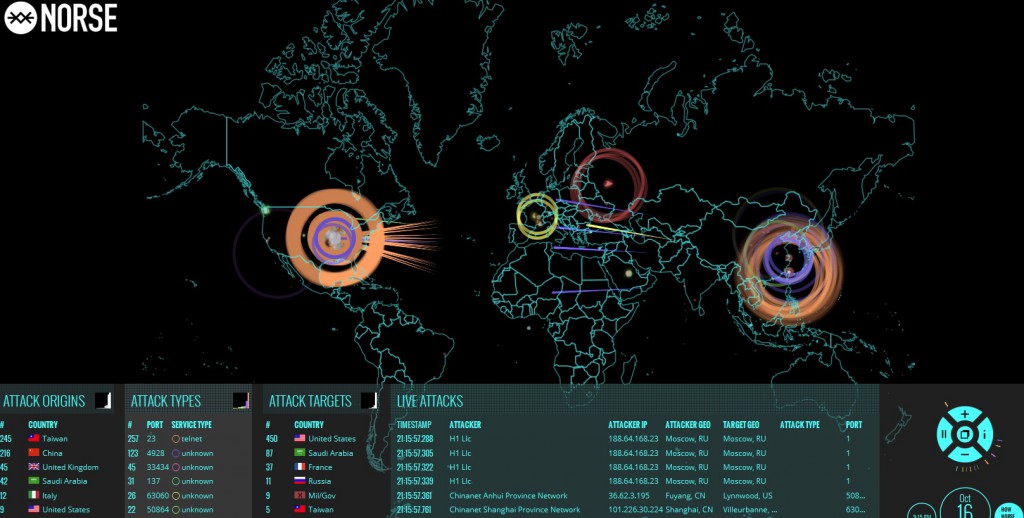
Link: http://map.norsecorp.com/
How it works:
Norse has a solid reputation in the security area, that’s why I believe that this cyber attack map is an accurate representation of the data they collect and monitor. What you are seeing on the IPviking site is live reporting of attacks reaching Norse’s honeypot.
2. Kaspersky Cyberthreat Map
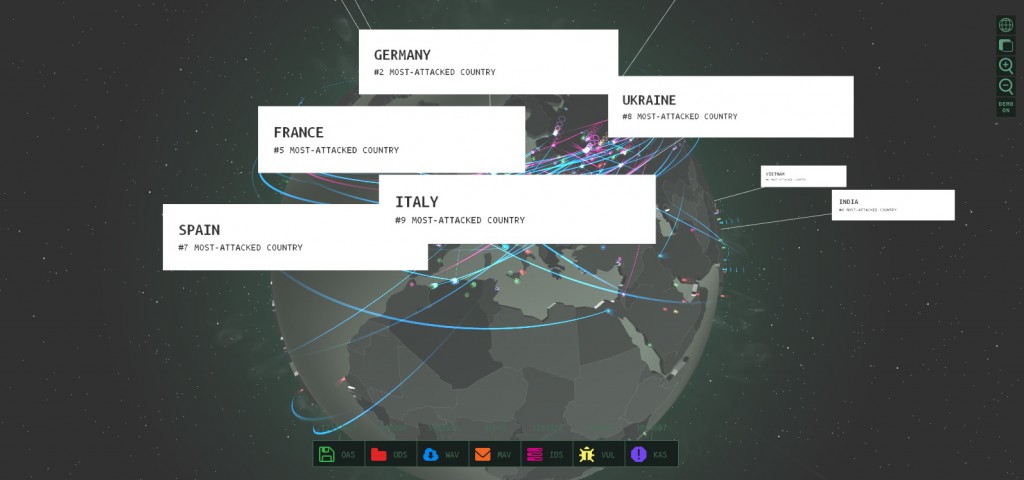
Link: https://cybermap.kaspersky.com/
How it works:
Kaspersky’s Cyberthreat map includes malicious objects detected during on-access and on-demand scans, email and web antivirus detections, and objects identified by vulnerability and intrusion detection sub-systems. This map presents real-time cyber attacks gathered by Kaspersky antiviruses from all the world.
1. FireEye Cyber Threat Map

Link: fireeye.com/cyber-map/threat-map.html
How it works:
Probably the most advanced system, FireEye uses a unique system of virtual machines that lets malware do whatever it wants and then shuts it down on the real network. In this way, no signatures are needed and even new attacks are caught before any significant damage occurs. FireEye have three components: an e-mail monitor, an internet traffic monitor and a control device that lets those two systems communicate with each other and work together to stop threats.
Conclusion
All of these maps state that they allow you to monitor cyber attacks in real time, but not all of them present detailed attacks, and not all of them are accurate. That’s why, I believe that at this moment we should only take the attacker and the victim countries as valid information. The number of attacks may also be accurate, but the precise source of the attack is hard to find. Anyway, the live cyber attack maps are pretty cool, a good marketing tool for big companies.