cyber attack Archive
Cyber attack on Lufthansa customer database
In Cyber Attack
Hackers had broken the database of the German Lufthansa airline customers, Der Spiegel newspaper, quoted by Agerpres. Lufthansa said it had taken prompt action, but admitted “that failed to prevent illegal access to records of customers’. According to Der Spiegel, unidentified hackers have accessed data site users, compromising their

Russian hackers have managed the most sophisticated cyber attack on the White House
A group of russian hackers managed to break the White House computer system, gaining access to private information which contain the program of US President Barack Obama, writes CNN. According to available information, the attack, behind which they may be Russian hackers, as stated by the authorities, was
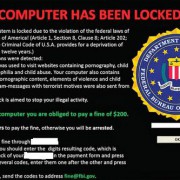
How to know if you have been hacked
81% of large businesses have suffered malicious data breaches shows in a cybersecurity survey, made by UK Government’s in 2014. That indicate almost one in five didn’t. “In this context, it’s impractical to prove a negative,” said Lenny Zeltser, a senior faculty member at the SANS Institute, who
Attorney-Client Privilege – Under Cyber Attacks
Law firms are the perfect targets for hackers according security experts. “It is almost a daily occurrence that we read about cyber attacks in the news. Unfortunately, on or around January 25, 2015, our firm was the victim of a single cyber attack, by a relatively new variant

Can driverless cars be hacked ?
Driverless cars could be vulnerable to hackers who could bring cities to a chaos, steal cars remotely or even commit deadly terror attacks, and many other problems, is a known fact. The report from the Institution of Engineering and Technology (IET) suggests that autonomous vehicles could be on the roads in

Dozens arrested in cybercrime raids
The UK’s National Crime Agency has arrested this week 56 suspected hackers as part of a “strike week” against cybercrime. In total, 25 separate operations were carried out across The United Kingdom. Those arrested are suspected of being involved in a wide variety of cybercrimes including data theft,

Tracking the FREAK ATACK, a huge SSL security flaw
Called Freak, Factoring attack on RSA-EXPORT Keys, the security breach exists on high-profile websites. It is supossed that seven hours is all it takes to crack the encryption that is in place on some supposedly secure websites. Browsers can be hijacked and tricked into accessing websites using legacy encryption. There was

Superfish: Lenovo is only the tip of the iceberg
In Malware
Security experts from G Data SecurityLabs analyzed Superfish adware. In this process, analysts have encountered in program, a technology component, called SSL digestion. It uses a root certificate which is poorly secured and has extensive rights on the computer. SSL Digestor intercept safe HTTPS connections which can be decrypted.

Federal Communications Commission approve net neutrality rules
The Federal Communications Commission on Thursday voted to approve new rules on how the internet should be governed. New rules will prohibit internet service providers from discriminating against content producers. “Who determines how you use the internet? Who decides what content you can view and when? Should there

Android phones can be tracked just with battery power alone
We all know that a phone uses more power the further away it is from a cell tower as it tries to connect. So, an Android phone can be tracked by studying their power use over time, without using their GPS or wi-fi/data usage. Extra power is used by